- Home
- Partnerships
- IDgo
IDgo leverages mobile device and encryption technologies to deliver a member authentication solution for all engagement channels that reduces the risk of impersonation fraud, improves operational efficiency and simplifies authentication experiences.
IDgo Enrollment – Member Experience
Credit union representatives complete a one-time member verification process that is recorded for future authentications as an encrypted credential associated with the member’s mobile phone security settings. This allows the phone to be used simply and securely for all future authentications.
IDgo Authentication – Member Experience
A notification is sent by a credit union representative to a member’s device, requiring the member to access their device to use the encrypted credential associated with their device security settings to authenticate.
| Use Case | Benefits |
|---|---|
| Contact Center, Chat | Faster and more pleasant member and staff experience, more secure verification process, representatives not burdened being "fraud detectors". |
| IVR | Callers authenticated before representative answers, saving average handle time and opening opportunity for authenticated members to self-serve. |
| AI Agent | Enables opportunity for members authenticated within AI Agent to self-serve transactions requiring authentication. |
| ITM | Enables opportunity for simpler, faster and more secure authentication thru ITMs. |
| In Person | Enables opportunity for simpler, faster and more secure authentication in person. |
IDgo leverages mobile device and encryption technologies to deliver a member authentication solution for all engagement channels that reduces the risk of impersonation fraud, improves operational efficiency and simplifies authentication experiences.
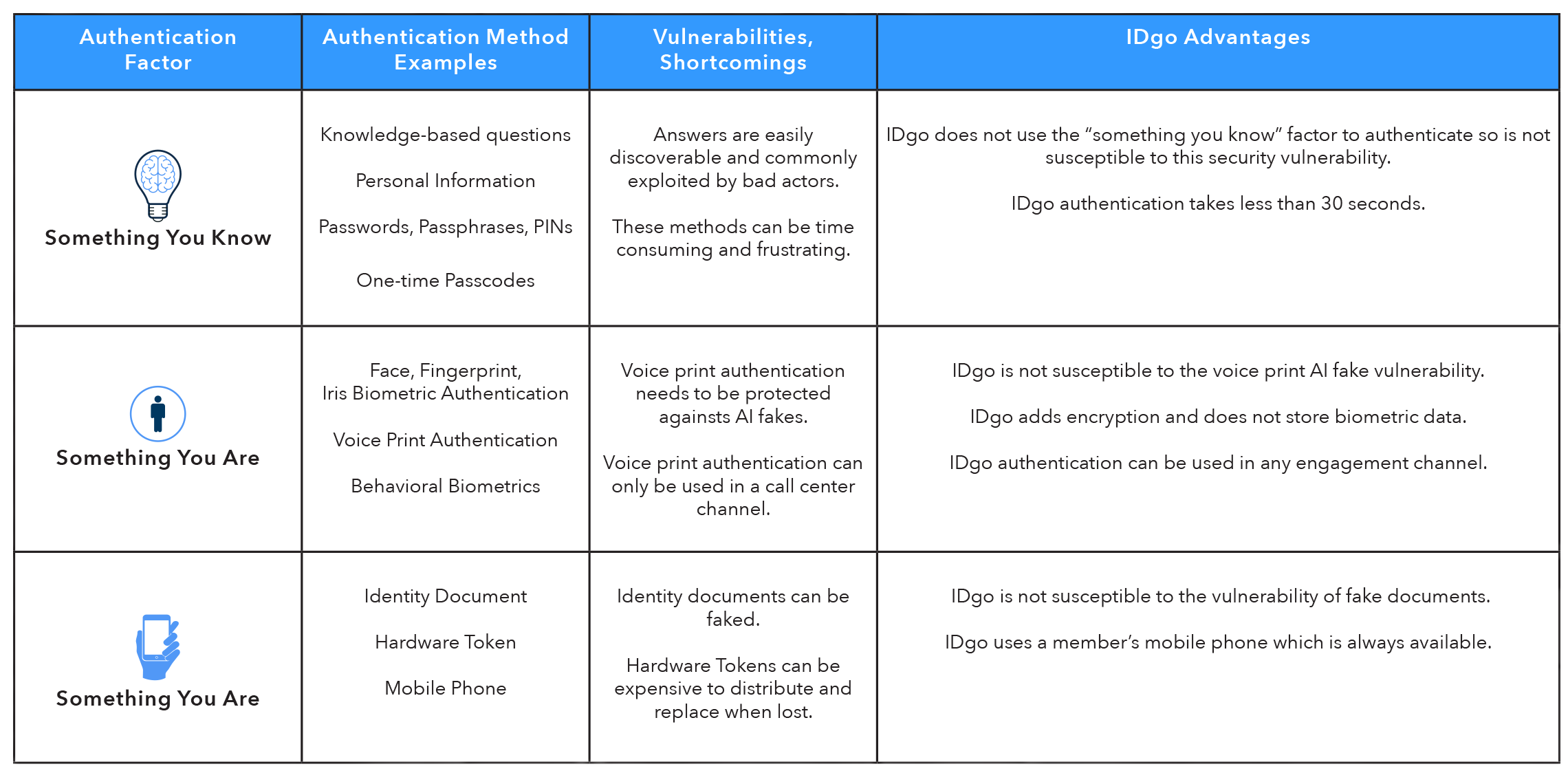
Member authentication typically relies on one or more than one of these three factors:
IDgo has been designed around “Something You Have” – a mobile phone and an encrypted credential. This is a device members carry every day, everywhere with powerful resident technology that can deliver a high level of security with a simple process. The table below illustrates advantages of IDgo over other authentication methods:
Faster, Frictionless Member Onboarding
Combat Fraud with AI-Driven Identity Protection
Increase Conversion Rates & Drive Growth
Seamless Integration with Core Banking Systems
Regulatory & Compliance Confidence
Simple & Secure Access
Mobile-First Convenience
Trust in Every Step
Account Login Multi-Factor Authentication - After entering username, password for online account, consumer uses IDgo to complete multi-factor authentication using an encrypted device credential.
Forgot Password - Before setting up a new password, consumer uses IDgo to authenticate using an encrypted device credential.
Step Up Authentication - Before executing risky transactions like a funds transfer, consumer uses IDgo to complete multi-factor authentication using an encrypted device credential.
Passwordless Account Login - Consumer uses IDgo to complete online account login using an encrypted device credential.
Call Centers, IVRs, In Person, Interactive Teller Machines, Anonymous Chat Sessions
Every authentication method relies on one of these three basic factors:
An essential part of the IDgo service is the consumer enrollment process, managed by participating enterprises:
Phishing, Smishing, Social Engineering, Credential Stuffing, Malware, Forgot Credentials, Brute Force Attack, Man in the Middle, Call Spoofing, SIM Swap
Resources include:
To fulfill your request, please provide the following:
* = Required field.
Close